This post is part of our course Adversary Emulation 101: Mimicking a real-world cyber attack.
If you want to beat your adversaries, think like them. A common adage we have all heard. MITRE ATT&CK is just that. A framework to think like adversaries and beat them in their game. It is a culmination of years of efforts of studying various cyber Adversaries’ Tactics, Techniques and turning them into Common Knowledge (ATT&CK).
What is ATT&CK framework?
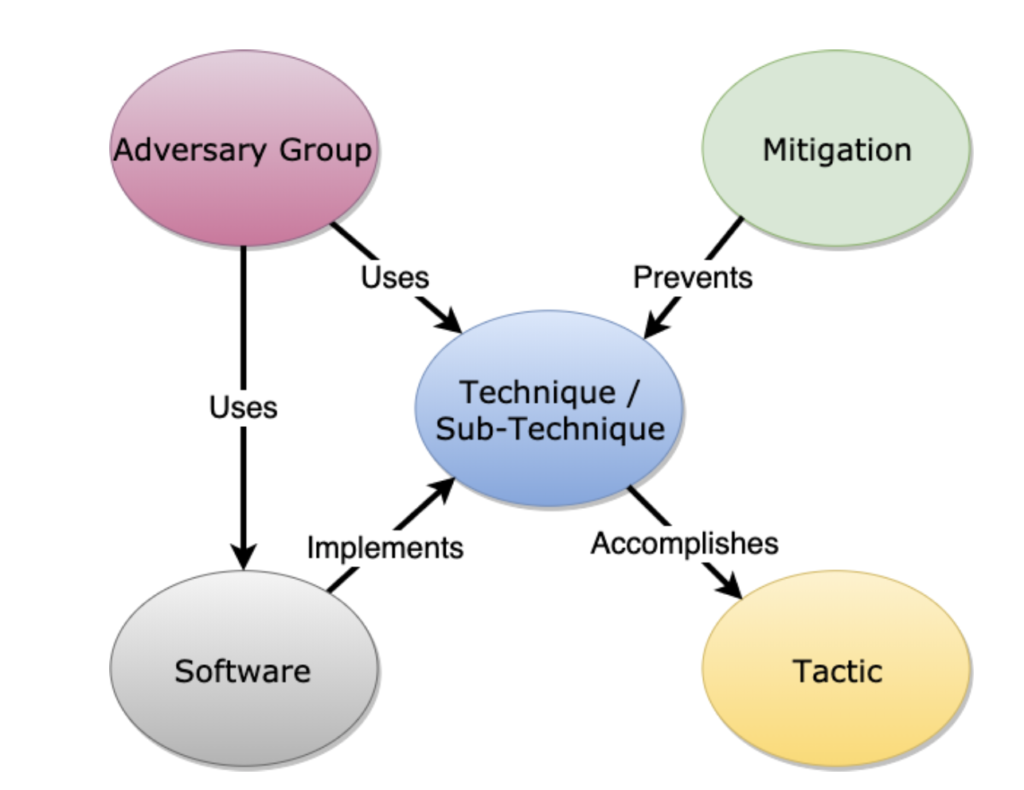
As per ATT&CK’s design and philosophy document, ATT&CK is a behavioral model that consists of the following core components:
- Tactics, denoting short-term, tactical adversary goals during an attack;
- Techniques, describing the means by which adversaries achieve tactical goals;
- Sub-techniques, describing more specific means by which adversaries achieve tactical goals at a lower level than techniques;
- Documented adversary usage of techniques, their procedures,and other metadata;
- Software, used by adversaries to implement a technique or a sub-technique; and
- Mitigations, preventing adversaries from achieving their tactical goal by blocking the execution of a technique or a sub-technique.
The following figure will help in understanding the relationship between various ATT&CK components.
Why was ATT&CK created?
MITRE’s goal behind creating this framework was to improve post-compromise detection of threats by tracing out the steps that could have been taken by an adversary. It was born out of the need to categorize adversary behavior as part of conducting adversary emulation exercises within MITRE’s Fort Meade Experiment (FMX) research environment.
What does it contain?
There are three variants of ATT&CK framework:
Originally, the Enterprise variant focused only on Microsoft Windows. However, later it was expanded to include macOS, Linux, PRE, AWS, GCP, Azure, Azure AD, Office 365, SaaS, Network platforms as well.
Each variant contains various tactics, techniques, sub-techniques and procedures that could be used by an adversary. The best way to visualize the framework is ATT&CK Navigator. It is an interactive web application, through which you can create layered views of the framework, as per your requirement.
Use cases
ATT&CK can be used for various purposes, such as:
- Adversary emulation
- Red teaming
- SOC assessments
- Defensive gap assessments
- Behavioral analytics development
- Cyber threat intelligence enrichment
MITRE provides an excellent getting started guide that shows how to utilize ATT&CK framework for these use cases.
Uday Mittal is a cybersecurity professional with rich working experience working with various industries including telecom, publishing, consulting and finance. He holds internationally recognized certifications such as CRTP, OSCE, OSCP, CISSP, CISA, CISM, CRISC among others. He speaks on cybersecurity awareness, offensive security research etc. and has authored various articles on topics related to cyber security and software development for a leading magazine on open source software.
