In this video, we give you a peek into the world’s supreme intelligence gathering tool, XKeyScore. Developed by the NSA, XKeyScore has been widely criticized ever since it’s existence became known through the documents leaked by Edward Snowden in 2013. Watch the video till the end to know why.

What you need to know about XKeyScore: NSA’s Mass Surveillance Tool

7 Ways to Cover Your Device’s Camera
Have you ever wondered that somebody might be watching you through your laptop’s webcam or smartphone’s camera? Or that while your laptop or smartphone stays on, in your bedroom, somebody might be recording your each and every act? Cracking into device cameras has been around ever since they were commercialized. Most of the devices we […]

Mr. Robot: Fsociety deploys ransomware
If you’ve been following the news, you would have come across a term called Ransomware. It is a type of computer virus which uses encryption as a weapon for destruction rather than protection of data. It encrypts files on an infected system and then demands a ransom, from the user of the infected machine, to decrypt […]

Hamazing 5: Hackers Who Inspire
Who are hackers? Contrary to the popular belief, hackers are curious souls interested in knowing the mechanics of things around them. With the advent of computers, a new generation of hackers were born. These are the people who willingly burn the midnight oil to grasp the nitty-gritty details of the white box (or whatever color […]
DDoS Attacks: When Servers Won’t Serve
DDoS stands for Distributed Denial of Service. DDoS is a type of attack in which multiple computers (for example a botnet) are used, to flood a single computer or a network with non-legitimate service requests to overload its resources. It is rare that a week goes by without news of some organization being impacted by […]
7 Cardinal Sins: Password Edition
On a normal day, an average computer user is required to input password to at least five different places (Windows, e-mail, social media, online banking, e-commerce). More often than not these passwords are same and are hardly changed once set. Passwords are the most abused and vulnerable security technology yet they can’t be replaced. They could […]

CISM: Everything You Need to Know
With 11th June, 2016 approaching fast, I am sure many of our aspiring readers would be looking for information on Certified Information Security Manager (CISM) certification. Wouldn’t it be beneficial, in terms of time and effort, if you could get all your questions answered in one place? Wait! You’re at that place already. Given the […]

Make Remote Access Your Ally
Today, every organization, big or small, is looking for a way to increase the productivity of their employees. They offer employees various kinds of flexibility options to help them achieve the much sought after work life balance. One such option is providing remote access to corporate network. Through this functionality employees can access their office […]
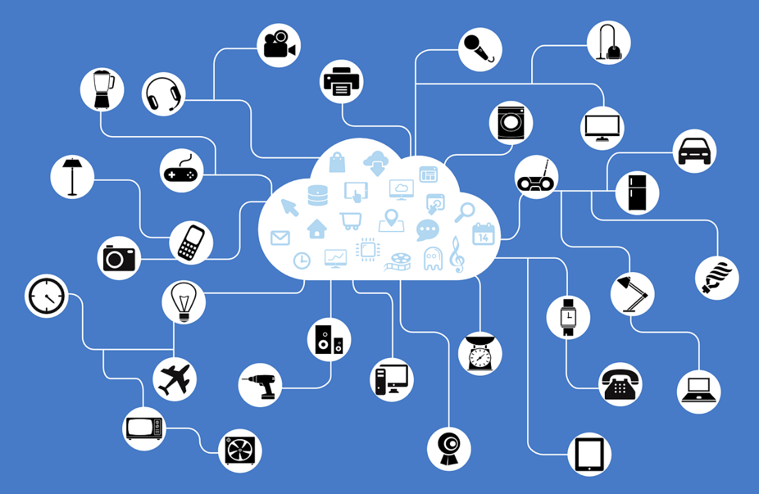
Hacking the Internet of Things: How Easy Is It?
One of the buzzword in the tech world these days is the Internet of Things and the idea behind it is that in near future all of our home appliances (among other things) will be connected to the internet and controlled by it. We will be able to set our toasters from our smartphones. Our […]
Anonymous India Strikes Back
Whether it’s cricket ground or battle-ground, things always heat up when the two sides are India and Pakistan. Off late, they’ve found a new frontier to battle, the cyber-ground. Both the nations have been in the state of unofficial cyber-warfare since 2010 and it doesn’t seem to end any time soon. Yesterday, a Pakistani hacker by […]
- « Previous Page
- 1
- …
- 4
- 5
- 6
- 7
- 8
- 9
- Next Page »